WikiLeaks Unveils Poor Password Practice From Sony Hack

Once again, Sony Pictures is facing a security compromise, and this time it isn’t a North Korean replying to “The Interview.” WikiLeaks has uploaded over 30,000 documents and over 100,000 emails curtailing from last year’s cyber attack on Sony Pictures.
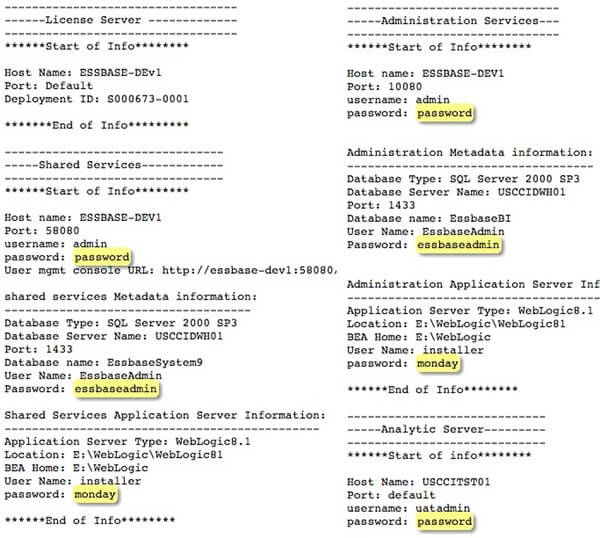
It is pretty embarrassing for such a leader in the entertainment industry to not use secure password practices. In fact, they had passwords that even a preschooler wouldn’t keep. Here is an instance where you can see how petty mistakes they’ve made are.
Most passwords are actually the word “password,” while the rest are either a day of a week or the user name itself. These easy-to-guess passwords don’t require some cracking software, even a school-goer would have guessed such passwords. These were extracts of some of the documents released by WikiLeaks. The e-mails too had several glitches like this and the personal stuff of the employees.
To save them from further embarrassment, the co-CEO, Michael Lynton said:
The cyber-attack on Sony Pictures was a malicious criminal act, and we strongly condemn the indexing of stolen employee and other private and privileged information on WikiLeaks. The attackers used the dissemination of stolen information to try to harm SPE and its employees, and now WikiLeaks regrettably is assisting them in that effort. We vehemently disagree with WikiLeaks’ assertion that this material belongs in the public domain and will continue to fight for the safety, security, and privacy of our company and its more than 6,000 employees.
If Sony can make such trivial mistakes, so can you. So don’t feel haughty about this and ask yourself whether you or your company have taken the requisite steps to avoid something like what Sony has faced.