Seven Must Have Internet Privacy and Online Security Tools- India
Seven Must-Have Internet Privacy and Online Security Tools
Information Security and Internet Privacy have become two of the greatest concerns today in the digital era. Why? Mostly because (as far as India is concerned), the Information Technology Act, 2000 and Rules do not adequately govern Internet privacy. The GDPR’s ‘Right To Be Forgotten’ initiative is lauded globally, and even got recognition in India with the landmark judgement Justice K.S. Puttaswamy v. Union of India in 2017. However, apart from its implicit recognition in the ambit of Article 21 of the Indian Constitution, the right is yet to be understood and exercised.
Given the known facts that India is such a huge internet market, it is disappointing that the levels of information security awareness and Internet privacy among people is abysmal. The pending status of the Digital Personal Data Protection Bill, 2022, does not provide hope for the long discussions around data protection regulations.
For these reasons, we have compiled a list of seven must-have internet privacy and online security tools that internet users may use for safety, data protection and personal safety.
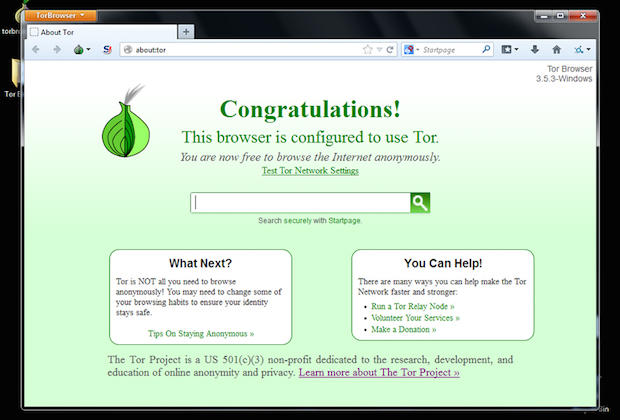
1. Tor Browser: (Download)
Known as the onion router, it is one of the best undefeated internet browsers (Well, nothing is bulletproof really). What happens when you communicate over a network is that packets bearing anything you send are transmitted. This browser uses relays to hide your identity from packets as much as possible. This does not mean you can use this for committing a crime because the reach of law enforcement is beyond those preying on you and this bit of edge is always a necessity.
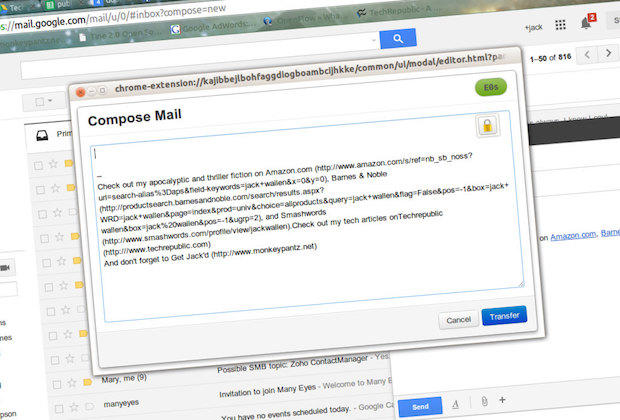
2. For Emails: (Download)
Either you could use PGP/GPG Encrypted email service or you could just take care that your passwords are strong and you have all security settings for your email done proper.
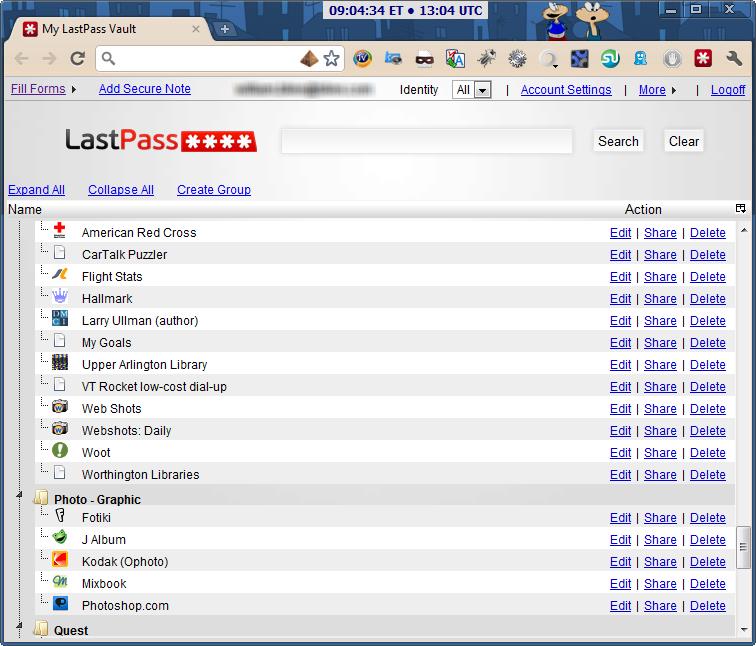
3. Last Pass:(Download)
This little tool here can do a lot of help to all those who are concerned about security but cannot remember too many passwords. Anyway, passwords is a key area of both Internet privacy and your online security and one which everyone talks about but still people don’t do much about it. The application creates a vault for you(which is encrypted) and once you login to your vault, all the passwords become visible as plain text. As soon as you logout, everything self encrypts again.
4. Ad Block: (Download for chrome)
While we guess most of you have it by now, you would have done it to avoid annoying ads and to bypass ones on YouTube. But more importantly this tool is important for you because you need to avoid the adware as well that are floating on the internet just as much and you can fall victim to them easily.
5. HTTPS Everywhere: (Download)
This tool is important given the current scenario in India, phishing crimes are on the rise even today. This plugin is available for most of the browsers and what it does is fairly simple. It forces the browser to load the secure version of any webpage over the normal version. This helps ensure that passwords are sent over an encrypted medium.
6. KeyScrambler: (Download)
This is one of those tools that secures each keystroke that you make i.e. encrypts it. In the free version it is only available for web browsers but guess that is enough to begin with. Keyloggers today are becoming obsolete unless an elite hacker is targeting you, so protecting keystrokes on the system is not as important as it is to protect keystrokes online.
.
7. Eraser: (Download)
Download this simple and straight utility to erase any file completely from your computer. It wdeletes a file and then rewrites the memory location with carefully selected patterns. As per its documentation available on the website:
- It Erases residue from deleted files
- Erases MFT and MFT-resident files (for NTFS volumes) and Directory Indices (for FAT)
- Powerful and flexible scheduler
All you need to do is right click on the file in place of delete use Eraser. If you are however a techie, you can always use command line utilities like sdelete.