Prevention and Control of Cyber Terrorism
Terrorism is continually changing. While at the surface, it remains “the calculated use of unlawful violence or threat of unlawful violence to inculcate fear.” In the wake of the recent computer attacks, a new breed of terrorism is on the rise and our country must defend itself with all possible means.
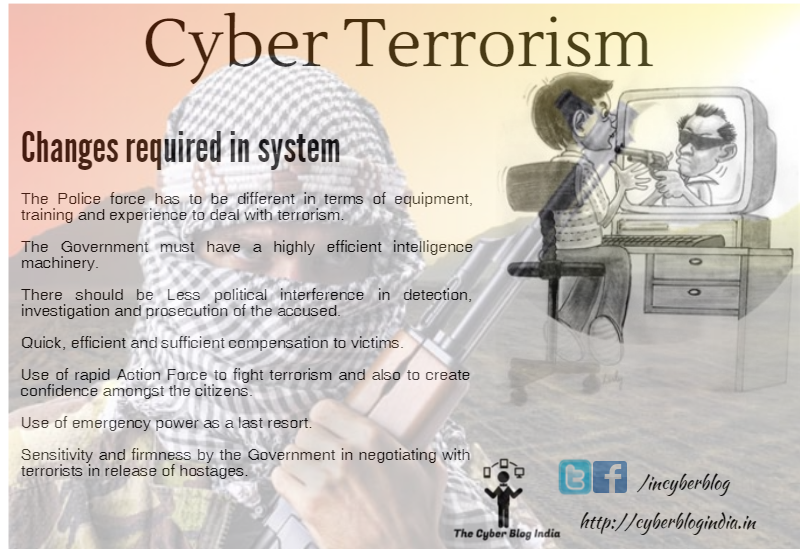
Cyber Terrorism
Cyber Terrorism may be defined as “the premeditated use of disruptive activities, or threat thereof, in cyberspace, with the intention to further social, ideological, religious, political or similar objectives, or to intimidate any person in furtherance to such objectives.”
Evolution of Cyber Terrorism
Cyber Terrorism can be traced back to June 1944’s attack on the communication system and logistic support of Germany. Thereafter, the USA Defense Department started Internet and Computer Networks and evolved the ICANN (Internet Corporation for Assigned Names and Numbers) system to regulate cyberspace. In 1988, Osama Bin Laden established “Al-Qaeda” based on “Jihad” and the same year, West German hackers accessed the Department of Defense Systems of the USA. Thereafter “Gulf War” was the first information war or I-war. By 1995, the Internet became popular through the World Wide Web in India and before that LTTE groups’ (militant groups that fought for a separate Tamil state between 1976 and 2009) activities were dependent on websites and the Internet.
Modes of Cyber Terrorism
- Attack on National Security: National security depends on confidentiality and secret information. When terrorists attack them, they delete or modify this information or purport to do the same.
- Cyber Terrorism is the Forerunner of Warfare: Warfare or NET warfare occurs when one nation causes terrorist violence against another nation using new technology.
- International Cyber Terrorist Attack: When international terrorist groups communicate with each other through the Internet to attack any nation then it may fall under an Internationally planned cyber terrorist attack.
- Network to Send Terror Message: Cybercriminals have started using technology to develop their own website to send terror messages and to communicate within or between groups.
- Digital Signature System: Terrorists use e-mail, SMS, encryption programs and digital signature systems to communicate securely and confidentially.
- Flowing Worm: Flowing “Worms”, Viruses, and Trojan Horses to collapse government and people interest sites, networks and computers is also one mode of cyber terrorism.
- Cyber Theft: Includes downloading illegal music files, and stealing millions of dollars from online bank accounts.
Case Study: Cyber Terrorism against Indian Parliament:
In the year 2001, the Indian Parliament was attacked with the help of information technology. The accused forged an official gate pass with the logo of the Ministry of Home Affairs and other information along with the layout of the Indian Parliament. Police found a laptop from the main accused Md. Afzal and S. Hussein Guru. They also found out that they did it through a Pakistani Internet Service Provider. They controlled the identity and E-mail system of the Indian Army.
Even the 11th September 2001 attack on WTC can fall under cyber terrorism. Terrorists had unauthorized access to the network of one airline and the hijacking of two airlines. This resulted in the crashing of those airlines into the WTC Twin Towers and the Pentagon.
Indian Legal Provision
The Information Technology (Amendment) Act 2008 has made the provision for cyber terrorism under Section 66F. It provides a Life Sentence, though the definition is not very comprehensive. This section is a combination of Section 66 [Computer-related offences] and Section 70 [Protected System] of the Act. What separates section 66F from other sections is the degree and nature of the offence.
Although there are many protective measures available for private corporations, there are several hurdles preventing corporations from implementing them:
- Firstly, implementing all of the necessary protective measures is expensive for private corporations. Depending on the size of the corporation, it could cost hundreds of thousands of dollars for a consultant to determine the corporation’s vulnerabilities and install protective measures.
- Secondly, determining a corporation’s computer systems vulnerabilities, installing security software, and upgrading it is very time-consuming. It takes time away from fostering the corporation’s business purpose and decreases profits.
- Thirdly, many of the security systems and complex technological advances in cyber-terrorism protective software are confusing and difficult to learn. It often takes a computer security specialist to determine what the corporation needs for security and how to install it.
- Finally, many private corporations do not want to report cyber-terrorist incidents to the authorities. It is embarrassing for a private corporation to have its network’s security breached.
