Kinds of People You Must Stay Away From, Unless You’re One
Cyber space is full of people trying to breach into some system, or to yank your personal stuff. As malware has come up a long way, so have these people who create them. So who are these bad guys? Why do they do so? Well, the answer to ‘why’ would attract a huge political and maybe, religious debate. But who are they?
Here are the seven most common kinds of cyber criminals in increasing order of threats. Recognize any?
1) Script kiddies: These are people who want to be hackers or think they are, but lack the technical skills required. They might hack a website that has very low security, or script a ‘virus’ that would eject your CD-drive every time you open it. They aren’t much of a threat, but still stay away from them.
2) Scammers: Ever checked your spam-box? It might be full of their works. From discount on Louis Vuitton shoes to claiming you can find a girl 8 kilometers away from your house, all these are what scammers do. They too aren’t much of a threat, but stay away from their emails.
3) Hackers: They usually work anonymously and create tools for hacking into computer systems. They often, but not always, hack computers without any criminal intent and are sometimes even hired by companies wanting to test their security. Hackers are a real threat, unless they work for you.
4) Phishers: They want your personal information and, most likely, your identity by directing you to deceiving websites. Sometimes, they work with scammers to send emails. They pose a great threat as their target area is very wide. Since they commit identity thefts, they don’t care whether it’s of a teenager from Mexico, or a 60-year-old Russian.
5) Political/religious/commercial groups: These people tend to not be interested in financial gain. They develop malwares for political ends, like Stuxnet worm reportedly created by a foreign government, which attacked Iran’s Atomic Program of its Nuclear Facilities. They are a great threat, but have limited target zone.
6) Insiders: They reside within an organization, and are considered as the highest risk because they remain anonymous and they cause a lot of damage to the company’s privileged information. Though, their area of operation is limited to an organization, they are responsible for maximum damage to the organization.After they’ve done their work, we find something like this:
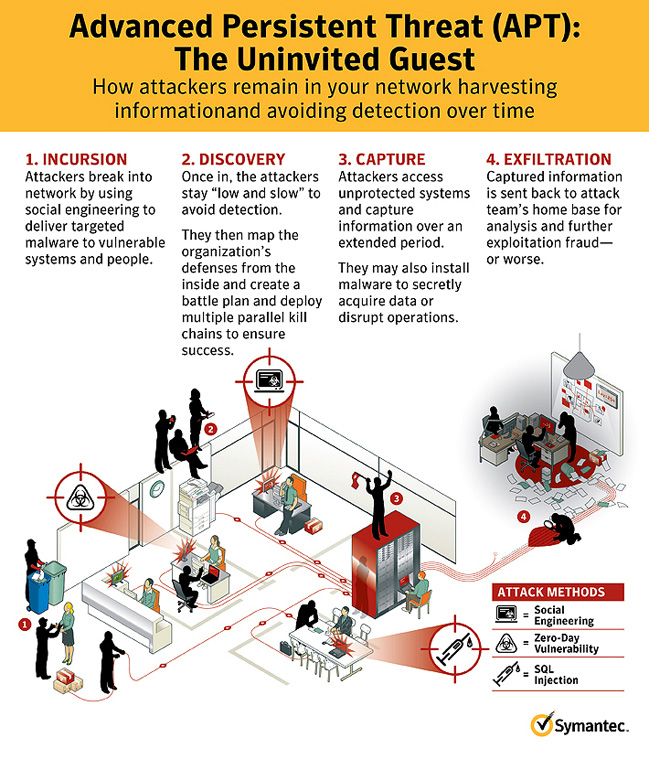
7) Advanced Persistent Threat (APT) Agents: They are a highly organized group that conduct targeted attacks. They are generally appointed by some high state-funded authorities. They have very deep technical skills, and can access vast resources from computers. Here’s something more about them:
So now you know, and as G.I.Joe would agree, it’s half the battle
To know how to stay away from these bad guys, stay tuned! And do check out some ways to avoid them if you’re using smartphones. You can also avoid threat to your personal stuff to some extent using 2-way authenticator.